A detailed investigative analysis of Telegram’s SIM card supply chain in Southeast Asia, examining how bulk SIM supply chains operate, why they persist, and why they matter in the context of global online fraud.
Introduction: Why SIM Cards Matter More Than Ever
SIM cards were once simple telecommunications tools. Today, they operate as digital identity anchors. A single SIM card can unlock access to messaging platforms, email accounts, ride-hailing services, social media profiles, cryptocurrency wallets, and even banking applications.
Because of this transformation, SIM cards have become high-value infrastructure assets. Whoever controls access to phone numbers often controls access to digital identities. This shift has made SIM cards increasingly relevant in discussions around cybersecurity, online fraud, and platform abuse.
While public attention often focuses on scam messages, fake profiles, or fraudulent transactions, far less scrutiny is applied to the upstream supply mechanisms that make such activity possible at scale. This investigation focuses on one such mechanism: Telegram’s SIM card supply chain in Southeast Asia.
Rather than alleging criminal intent, this article documents how SIM cards are marketed, distributed, and scaled through Telegram channels and why this layer of the digital ecosystem deserves closer examination.
Scope and Methodology
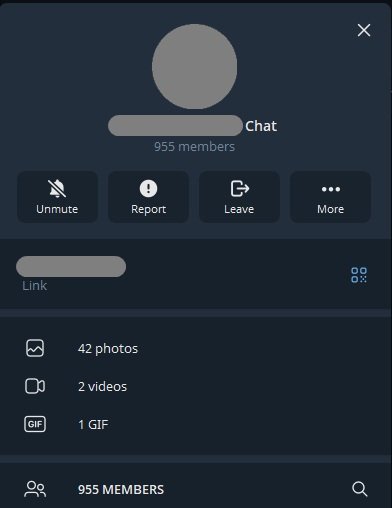
This investigation is based on a preserved export of a Telegram channel advertising bulk SIM cards and data SIMs in Southeast Asia, with repeated references to Cambodia and nearby jurisdictions.
Methodology and Ethical Framework
- The dataset consists of original Telegram messages, images, and timestamps.
- All visual evidence used in the publication is redacted to remove personal identifiers.
- Non-English messages are translated literally, without reinterpretation.
- No attempt is made to identify individual buyers or sellers.
- The focus remains strictly on infrastructure, market behaviour, and systemic patterns.
This approach aligns with established investigative journalism standards and ensures factual accuracy without overreach.
Telegram as a Distribution Platform
Unlike conventional e-commerce platforms, Telegram offers an environment with minimal onboarding friction. Channels can be created quickly, administrators can remain pseudonymous, and content can be replicated across multiple channels with little effort.
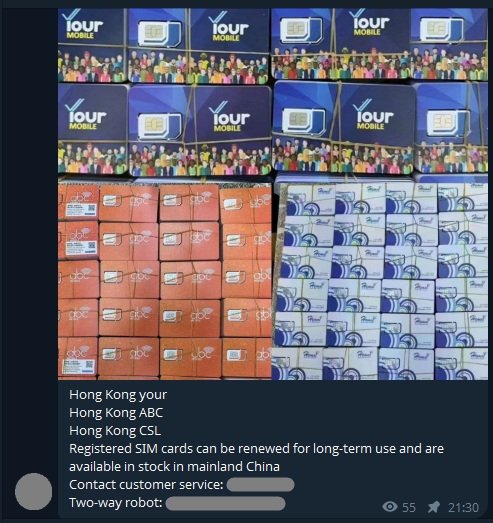
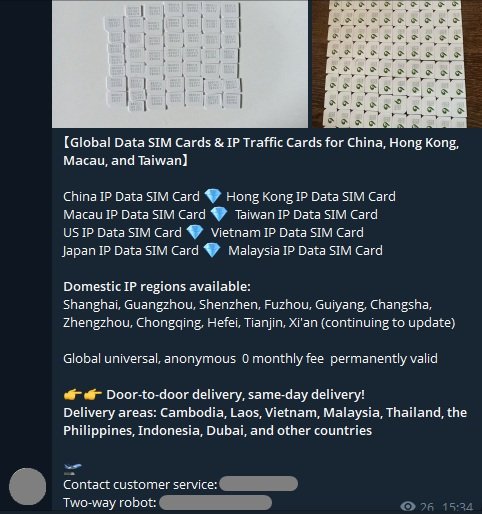
In the examined dataset, Telegram functions less like a social network and more like a digital trade bulletin. Posts follow a repetitive, transactional format:
- Product images (often showing SIM cards in bulk)
- Brief availability statements
- Direct contact instructions
There is minimal conversational interaction and no attempt at consumer education. This strongly suggests a business-to-business orientation rather than retail sales.
Historically, similar structural characteristics have been observed in other informal digital markets, particularly those operating in regulatory grey zones. Telegram’s channel architecture, persistence, and replication capability make it well-suited for such use cases.
Channel Mechanics and Market Persistence
A notable characteristic of the dataset is continuity. Advertisements appear at regular intervals, often using near-identical phrasing and visual layouts. This repetition suggests an ongoing supply operation rather than isolated resale events.
Key structural observations include:
- Standardised language across multiple posts
- Recurring product imagery, sometimes reused
- Absence of promotional discounts is typical of consumer markets
- No customer support language, warranties, or refund policies
These traits are consistent with wholesale supply environments, where speed and volume matter more than branding or customer experience.
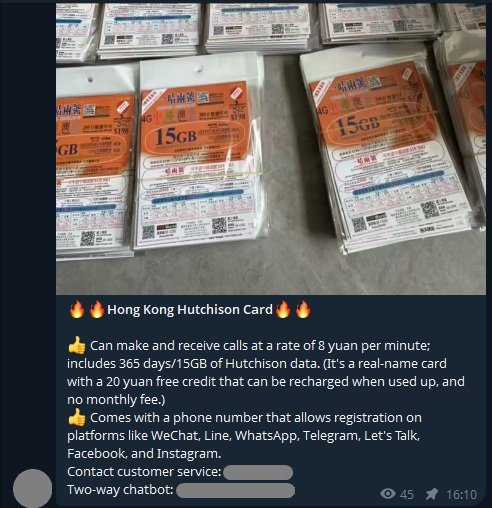
Commercial Scale and Visual Indicators
Images within the dataset frequently show large quantities of SIM cards, often stacked, packaged, or grouped. In legitimate retail contexts, SIM cards are typically sold individually, accompanied by operator branding and activation instructions.
By contrast, the material examined here emphasises:
- Quantity rather than features
- Availability rather than compliance
- Speed rather than service
Such emphasis provides important context when evaluating how these markets operate.
SIM Cards as Digital Identity Infrastructure
To understand why SIM card supply chains attract attention from cybersecurity researchers, it is necessary to understand how SIM cards function within modern digital systems.
SIM cards are commonly required for:
- One-time password (OTP) verification
- Messaging app account creation
- Account recovery processes
- Multi-factor authentication
As a result, many online platforms implicitly treat possession of a phone number as a proxy for identity. When phone numbers become easily replaceable or disposable, this trust model weakens.
Public reports from international organisations and cybersecurity firms have repeatedly documented how large-scale fraud operations depend on high-volume SIM access. This investigation does not assert that the observed sellers are participating in such operations. Instead, it documents a supply layer that has been widely identified as necessary for those operations to exist.
Language, Positioning, and Market Signalling
The phrasing used in the dataset is concise and utilitarian. Messages prioritise availability and quantity, often omitting price details or regulatory context.
This linguistic economy is itself informative. In wholesale markets, language tends to focus on:
- Inventory status
- Delivery readiness
- Contact efficiency
By contrast, consumer-facing markets typically include explanations, reassurances, and promotional language. The absence of such features reinforces the interpretation that these channels serve a specialised audience.
Geographic Focus and Regulatory Fragmentation
The dataset repeatedly references Southeast Asian jurisdictions, particularly Cambodia. This regional focus aligns with broader reporting on telecom regulation variability across the region.
Several structural factors are relevant:
- Inconsistent SIM registration enforcement
- Cross-border resale of telecom products
- Limited coordination between national regulators
When SIM cards move across borders faster than regulatory oversight, enforcement becomes fragmented. Even where regulations exist, practical enforcement may lag behind market behaviour.
The Platform–Telecom Responsibility Gap
One of the most persistent challenges highlighted by this investigation is the division of responsibility between platforms and telecom providers.
- Messaging platforms often argue they merely host content.
- Telecom operators emphasise compliance with local registration rules.
- Regulators face jurisdictional and technical constraints.
This diffusion of accountability creates spaces where supply chains can operate with limited scrutiny, even when downstream misuse is widely acknowledged.
What the Evidence Shows and What It Does Not
It is essential to define the boundaries of this investigation clearly.
What the Dataset Shows
- Persistent advertising of bulk SIM cards
- Commercial scale indicators
- Regional focus and repetition
- Platform suitability for such markets
What the Dataset Does Not Show
- Individual scam operations
- Victim interactions
- Direct evidence of criminal intent
By maintaining this distinction, the investigation remains focused on documenting infrastructure, not assigning blame.
This video was sourced from a public Telegram channel and edited solely to remove identifying information. Its inclusion does not imply intent or downstream use.
Why This Supply Layer Matters
Discussions around online fraud often concentrate on reactive measures: account bans, content moderation, or victim education. While necessary, these approaches address symptoms rather than causes.
SIM card supply chains represent a foundational layer. When access to phone numbers is abundant and easily replaced, downstream enforcement becomes significantly more difficult.
Understanding how these supply mechanisms operate is therefore critical for policymakers, platforms, and researchers seeking durable solutions.
Editorial Note and Series Context
This article serves as the pillar for a broader investigative series examining digital infrastructure abuse, regulatory blind spots, and upstream enablers of cybercrime.
Subsequent articles will explore:
- Telegram’s role as infrastructure
- The economics of bulk SIM distribution
- Telecom KYC weaknesses
- Enforcement challenges and policy gaps
Each article will link back to this pillar to provide context and continuity.
Sources & References
This investigation draws on publicly available international reports, academic research, and primary-source Telegram data preserved by the author. All translations are literal, and all identifying details have been redacted.
- Cyber-Enabled Fraud and Financial Crime
United Nations Office on Drugs and Crime (UNODC)
https://www.unodc.org/documents/Cybercrime/Cyber-enabled_fraud_and_financial_crime.pdf - Misuse of Prepaid SIM Cards for Criminal Activities
Europol
https://www.europol.europa.eu/publications-events/publications - Mobile Phone Registration: Global Review
GSMA
https://www.gsma.com/mobilefordevelopment/resources/mobile-phone-registration/ - Weak KYC Controls and Digital Fraud Risks
Financial Action Task Force (FATF)
https://www.fatf-gafi.org/en/publications.html - Telegram Transparency Reports
Telegram
https://telegram.org/transparency - Pig Butchering Scams and Infrastructure Abuse
Chainalysis
https://www.chainalysis.com/blog/pig-butchering-scams/ - SIM Card Image (Conceptual)
Photo by Andrey Metelev on Unsplash
https://unsplash.com/photos/6LwmMV15Ug4
For deeper investigations on such topics, see our Cybercrime Investigations & Exposes.