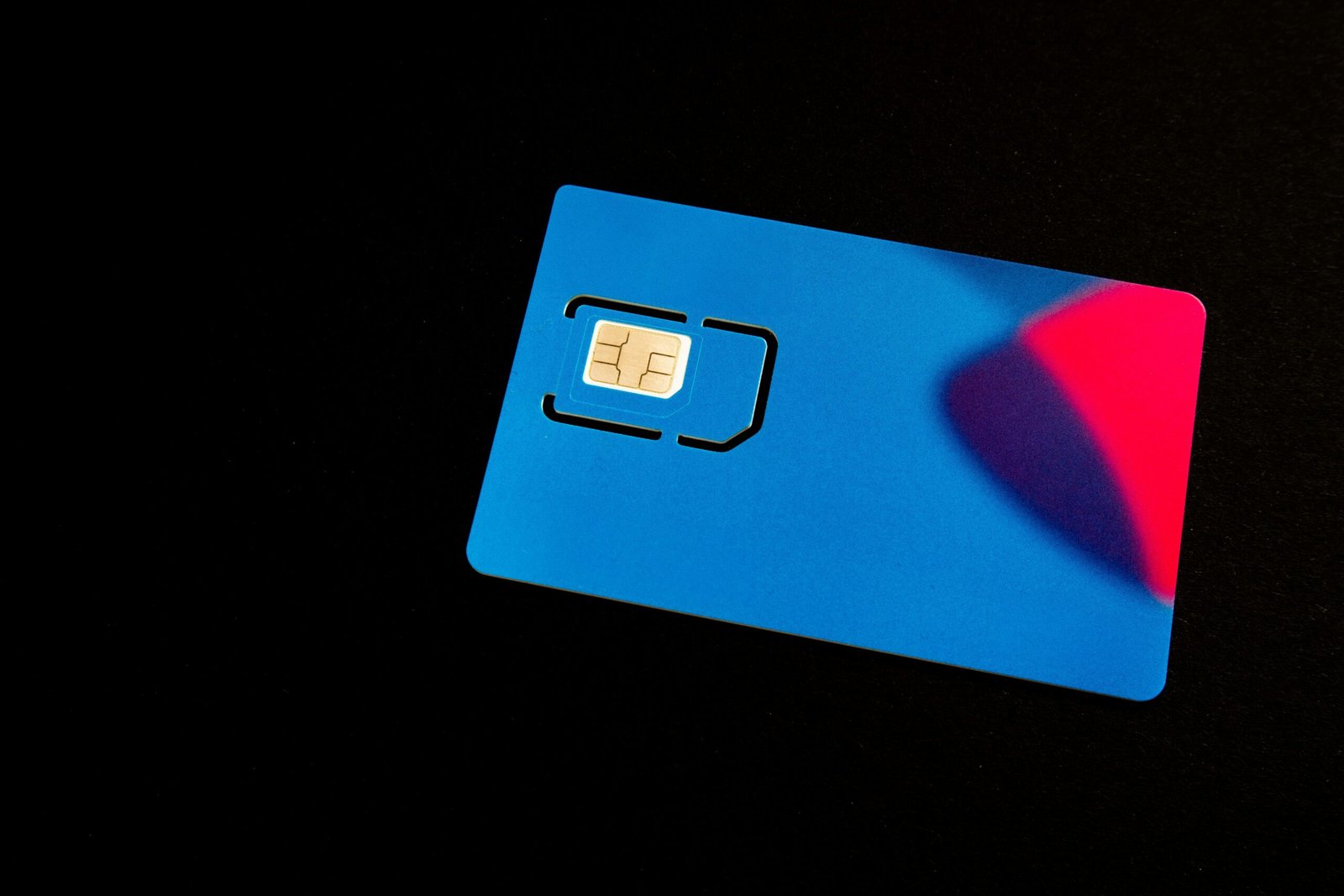
An investigative analysis of why SIM cards are central to scam operations, examining authentication systems, account lifecycles, and enforcement challenges.
Introduction
Public discussions about online scams often focus on messaging content: the fraudulent message, the impersonated brand, or the manipulated victim. This focus, while understandable, overlooks a more fundamental dependency shared by many scam typologies: the phone numbers and SIM cards used in online scams.
In modern digital systems, phone numbers function as identity gateways. They enable account creation, authentication, recovery, and persistence across platforms. As a result, access to SIM cards is not incidental to scam operations; it is structural.
This article explains why SIM cards occupy a central role in scam ecosystems, drawing on public reporting, platform design analysis, and cybersecurity research. It does not rely on allegations against individual sellers. Instead, it examines why demand for large volumes of SIM cards exists in the first place.
Phone Numbers as Digital Identity Anchors
Many online platforms implicitly treat possession of a phone number as proof of identity or legitimacy. This design choice simplifies onboarding and improves user recovery options, but it also creates a dependency.
Phone numbers are commonly required for:
- One-time password (OTP) verification
- Messaging app account creation
- Account recovery and re-verification
- Two-factor authentication (2FA)
In effect, a SIM card becomes a key that unlocks access to multiple digital services. When that key can be replaced easily, identity becomes fluid.
OTP Systems and Their Limits
One-time passwords sent via SMS are widely used because they are convenient and broadly accessible. However, SMS-based OTPs assume that:
- Each phone number maps to a single user
- Numbers are not easily disposable
- Access to numbers is regulated
In practice, these assumptions do not always hold. Where SIM cards can be acquired in volume, OTP systems lose much of their protective value. Accounts can be created, abandoned, and recreated with relative ease.
This is not a vulnerability in any single platform; it is a systemic design trade-off shared across the digital ecosystem.
Account Lifecycles in Scam Operations
Scam operations rarely rely on a single long-lived account. Instead, they manage account lifecycles:
- Create a large number of accounts
- Operate them until flagged or banned
- Discard and replace them rapidly
SIM cards are integral to this cycle. Each new account typically requires a fresh phone number, particularly on messaging platforms such as Telegram, WhatsApp, or similar services.
This explains why demand exists not just for SIM cards, but for high volumes of short-lived or interchangeable numbers.
Disposable Connectivity and Operational Scale
From an operational standpoint, disposable SIM cards offer several advantages to fraud networks:
- Parallelisation: Multiple accounts can operate simultaneously
- Redundancy: Loss of one number does not disrupt the system
- Geographic masking: Numbers from different regions can be rotated
These features allow scam operations to scale horizontally. The limiting factor is not content creation, but access to authenticated identities, which SIM cards provide.
Why Enforcement Often Targets the Wrong Layer
Law-enforcement and platform responses frequently focus on:
- Takedown of scam accounts
- Content moderation
- Victim awareness campaigns
While necessary, these measures address outputs, not inputs. As long as SIM cards remain readily available, banned accounts can be replaced faster than enforcement actions can propagate.
This asymmetry explains why many large-scale scam operations reappear quickly after disruptions.
Dual-Use Nature of SIM Cards
It is important to acknowledge that SIM cards are dual-use goods. They are essential for legitimate activities such as:
- Travel connectivity
- Device testing
- Business operations
The same properties that make SIM cards useful for legitimate purposes, portability, accessibility, and low cost, also make them attractive for abuse.
This dual-use nature complicates regulatory responses and underscores why the issue cannot be reduced to simple prohibition.
Why This Demand Shapes Upstream Markets
Understanding why SIM cards are central to scam operations clarifies why upstream supply markets exist at all. The bulk SIM trade does not emerge in isolation; it responds to structural demand created by platform design and authentication norms.
This does not imply that suppliers control downstream use. It does explain why SIM card distribution has become a strategic layer within broader fraud ecosystems.
What This Article Does Not Claim
For clarity:
- It does not claim that all SIM card resellers support scams
- It does not allege intent by specific suppliers
- It does not identify individual scam networks
The analysis remains focused on systemic dependencies, not attribution.
Conclusion
SIM cards sit at the intersection of telecommunications and digital identity. In scam operations, they function less as communication tools and more as identity tokens enabling access, persistence, and scale.
Any serious attempt to address large-scale online fraud must grapple with this reality. Without understanding why SIM cards are central to scam operations, enforcement efforts risk remaining reactive rather than structural.
This article contributes to that understanding as part of a broader investigative series on digital infrastructure and cybercrime enablement.
Sources & References
- Cyber-Enabled Fraud and Financial Crime
United Nations Office on Drugs and Crime (UNODC)
https://www.unodc.org/documents/Cybercrime/Cyber-enabled_fraud_and_financial_crime.pdf - Mobile Phone Registration: Global Review
GSMA
https://www.gsma.com/mobilefordevelopment/resources/mobile-phone-registration/ - Pig-Butchering Scams and Infrastructure Abuse
Chainalysis
https://www.chainalysis.com/blog/pig-butchering-scams/
For deeper investigations on such topics, see our Cybercrime Investigations & Exposes.